
Why Varonis' Cookie-Bite PoC Redefines Session Hijacking Threats
Discover how the Varonis Cookie-Bite PoC redefines session hijacking by stealing browser cookies to bypass MFA and maintain persistent access to cloud services like Microsoft 365.

Midnight Blizzard Exposed - Inside APT29's 2025 Grapeloader Campaign
We uncover the sophisticated tactics of the notorious APT29 group, also known as Midnight Blizzard. This deep dive explores their 2025 phishing campaign leveraging the advanced Grapeloader malware, targeting global organizations with precision. Learn how APT29 exploits vulnerabilities, deploys stealthy payloads, and evades detection, alongside expert insights into countermeasures to protect against this evolving cyberthreat.
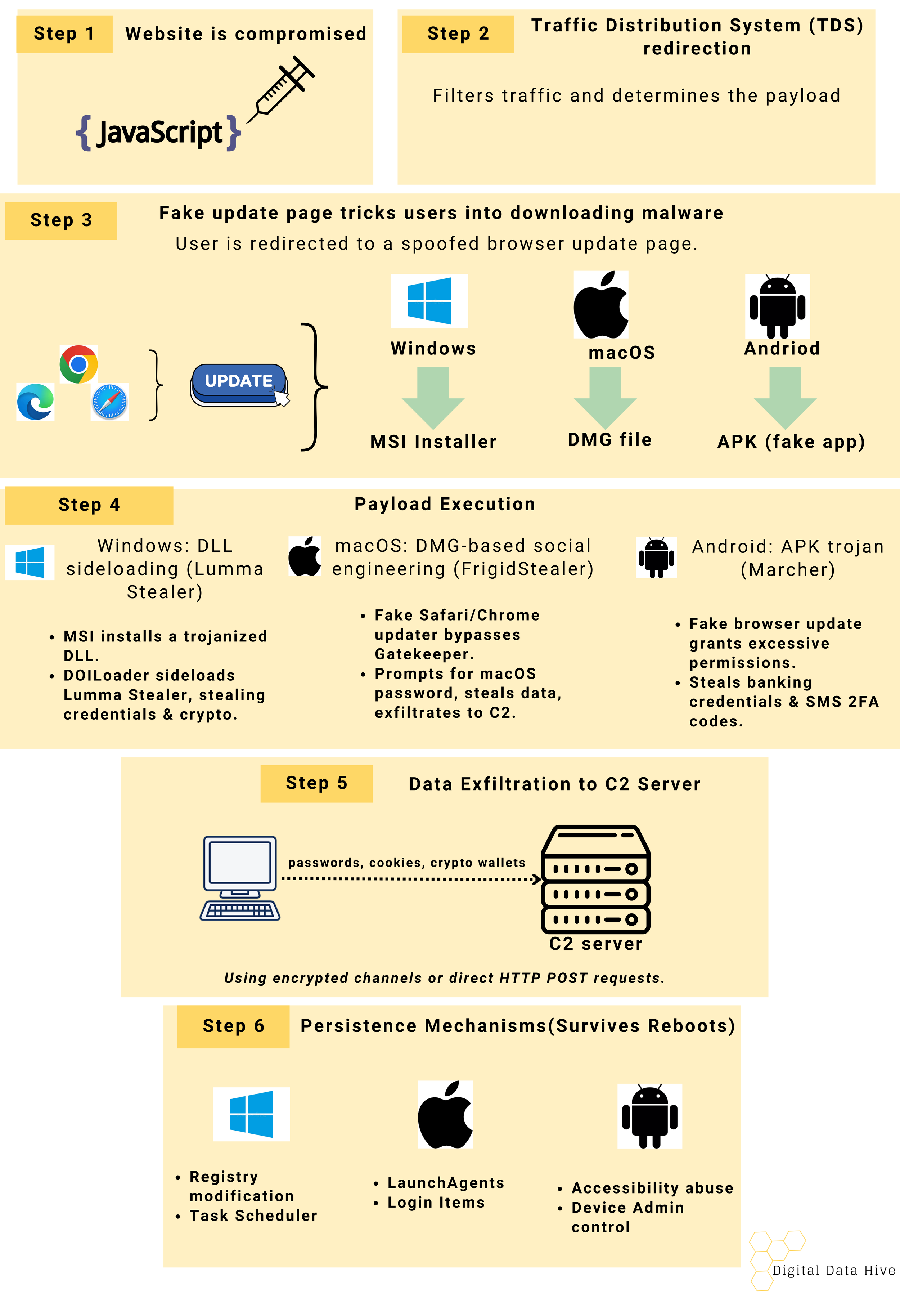
How Cybercriminals Use Web Injects to Deliver Malware: A Deep Dive into TA2726 & TA2727
Cybercriminals are using fake updates to deliver malware across Windows, macOS, and Android. Our latest blog breaks down the full attack chain in six steps, revealing how attackers compromise websites, trick users, and steal sensitive data.

How a Typosquatting Attack on BoltDB Exposed a Major Security Flaw in the Go Ecosystem
A recent typosquatting attack on Go developers disguised a malicious package as the popular BoltDB library, exploiting Go’s module caching system to keep the backdoor accessible even after the repository was cleaned.

Inside TA397’s Playbook - From Phishing Emails to RATs
TA397, also known as UAC-0001, uses phishing emails, malicious macros, and Remote Access Trojans (RATs) to target high-profile entities, primarily in Ukraine.

Inside Operation Digital Eye - How Hackers Used Legitimate Tools for Infiltration
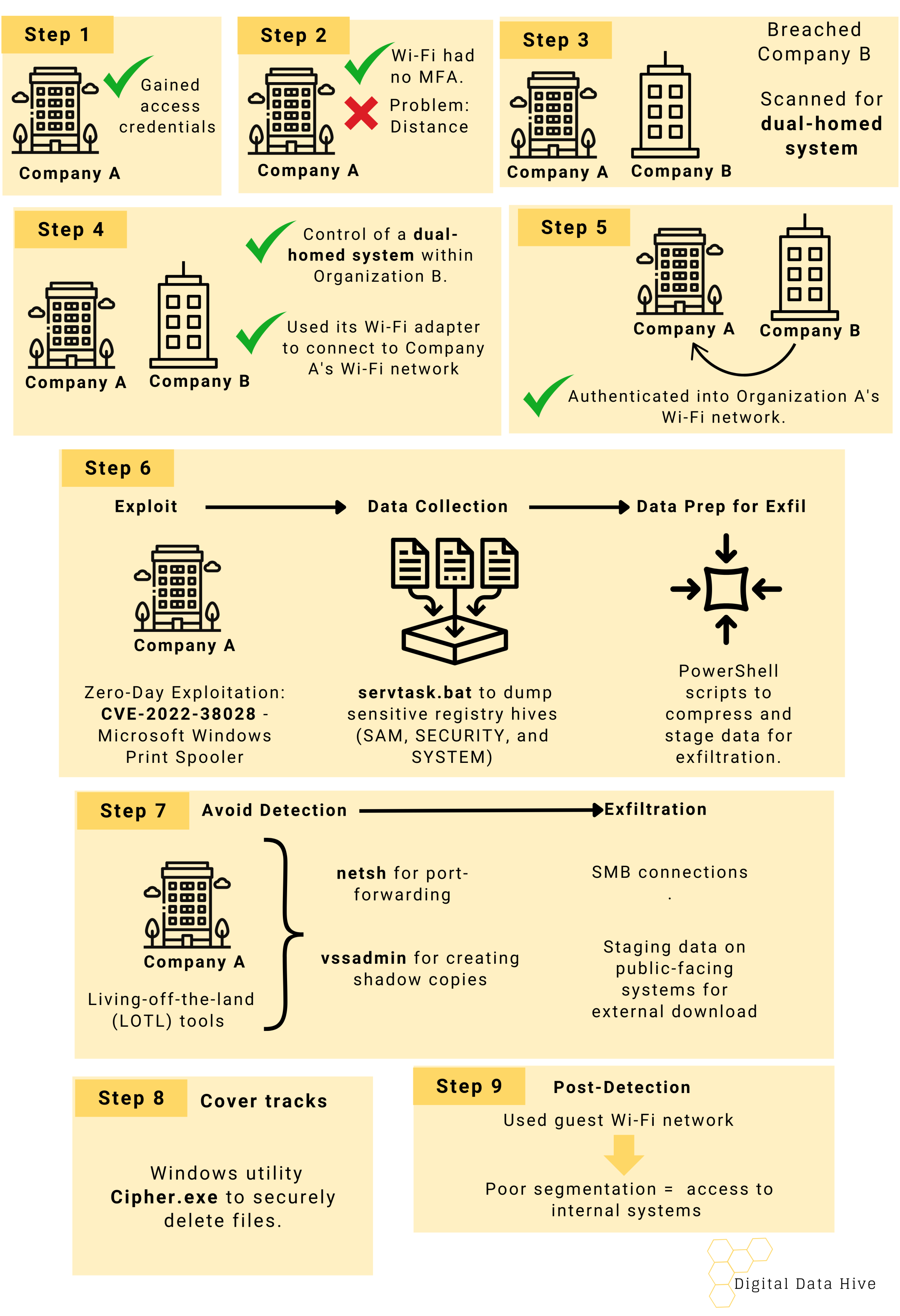
The Breach from Next Door. How Russian APT Exploited Wi-Fi to Infiltrate Their Target
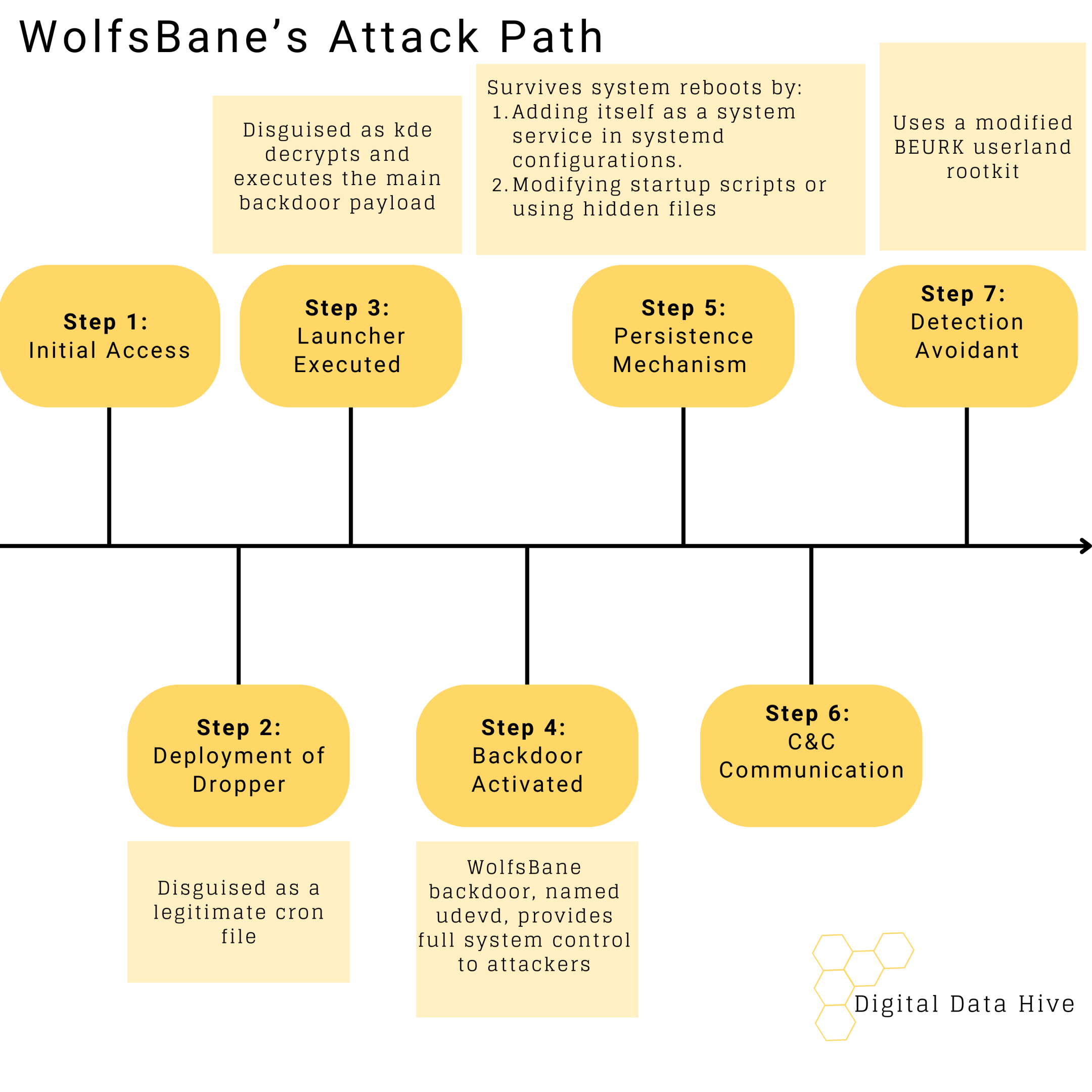
Beware the Wolf- WolfsBane Marks Its Linux Territory

Fortinet VPN Flaw: How Hackers Can Sneak Past Security Without a Trace

T-Mobile Breached Again: A Closer Look at Salt Typhoon’s Espionage Tactics

Did Apple Lie to Us? The Truth Behind M-Series Chips' Security Promises.

Scattered Spider is Causing Arachnophobia

Elevating Cybersecurity with NIST CSF 2.0

Cybersecurity - A Pillar of Modern Business - According to the CISA

Understand your Network - Simplifying Netstat with the Network Top Processes Program!

The Art of Transcription: Decoding Videos for Deeper Insights in Digital Forensics
Beyond the Surface: The Hidden World of Email Headers in Digital Forensics

Navigating the Aftermath: Dealing with the Impact of an Application Security Breach
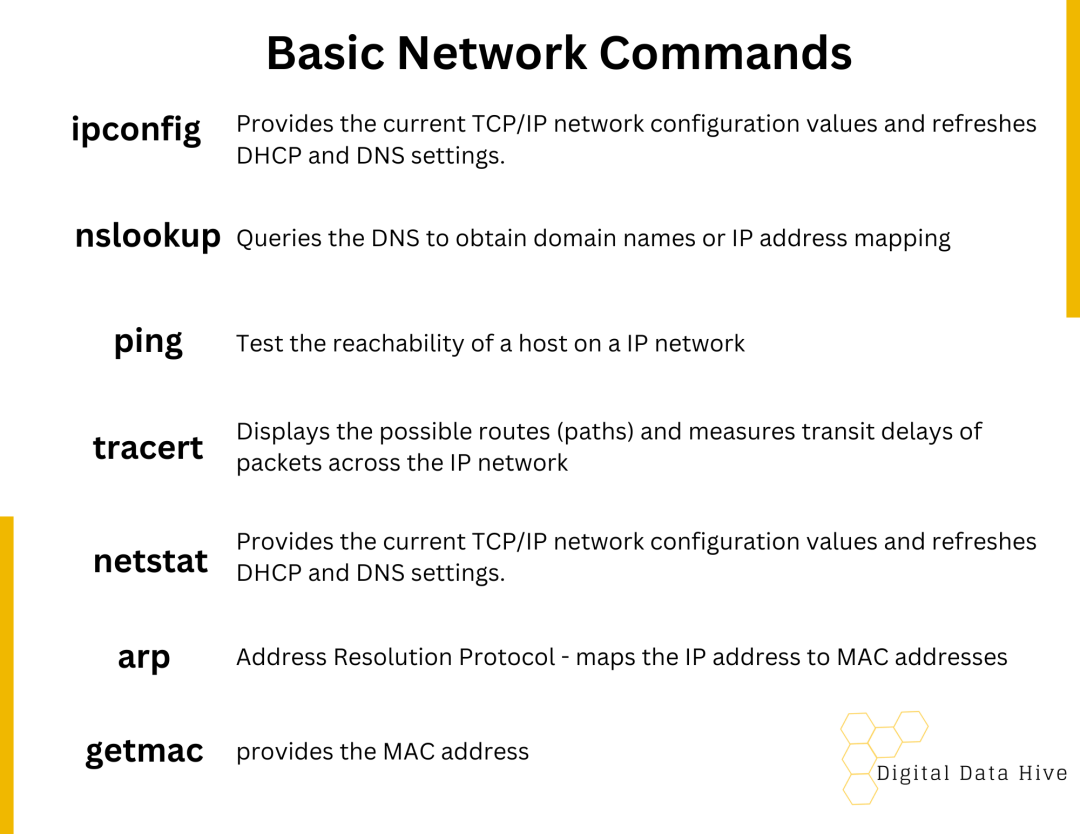
Network Forensics Basics

